These Make Us Think.
This is information worth sharing.
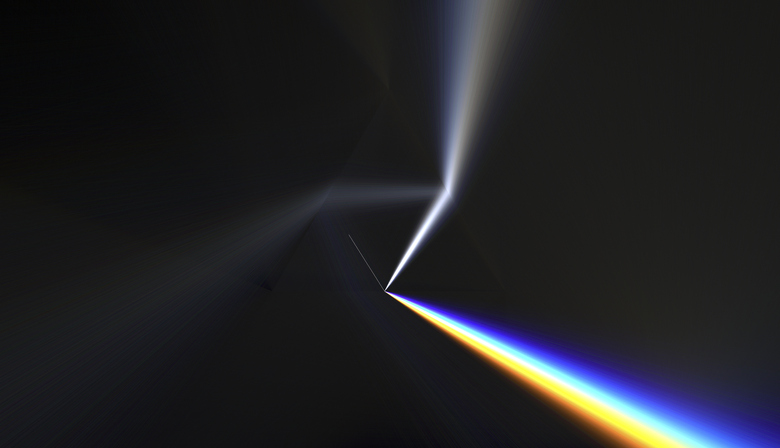
PRISM
The Internet has given us nearly unlimited access information of all kinds. We can learn about anything that interests us with a few clicks. So can our government, and when their topic of interest is your internet use, that’s a concern.
The federal government’s primary tool for monitoring the Internet activity of U.S. citizens is an initiative called PRISM, launched in the years following 9/11 and immediately covered up. Few people knew anything about it until 2013, when whistleblower Edward Snowden exposed it.
PRISM isn’t an acronym; instead, it’s a codeword that summarizes the government’s attempt to take large quantities of information and focus it in specific areas. In particular, PRISM allows the government to obtain information about individual users directly from the Internet’s biggest sites, such as Google, Facebook and YouTube. Also included in PRISM’s surveillance is mobile data, including location information and text messages.
The government claims that it only does this surveillance to ensure the safety of its citizens, and that PRISM only collects data when there is a given reason to look at the activity of a particular user. However, just as your Echo Dot can hear your conversations when you haven’t specifically said “Alexa”, there’s no guarantee that the government isn’t watching more of your Internet activity than you’re aware of.
Critics of PRISM claim that the program is unconstitutional. The truth is, we don’t really know what the government is doing with our data. The data may simply help the government to identify legitimate issues that might otherwise have gone unnoticed. Or, the government may be compiling data to one day be used against us. Since there is so much grey area surrounding PRISM, which the government has neglected to clarify, many people assume the worst.
What should you, a law-abiding citizen, do about PRISM? Treat your personal data carefully. Protect it. Use safeguards wherever possible, including VPNs, data encryption and private browsing. Be wary of public wifi networks and online storage tools. Above all, be aware of the threats surrounding you, and make choices regarding you and your family’s Internet privacy knowing what’s lurking just out of sight.



